Fortify API Credentials
In order to integrate Security Phoenix with your Fortify account, you’ll need to authorise the platform to access Fortify REST API. The following steps describe how to create the required API access credentials.
Create a Personal Access Token
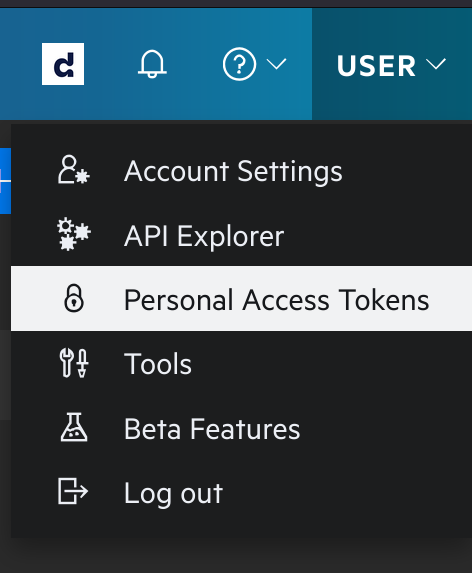
In your Fortify interface, locate and click on the User entry on the top-right of the screen. In the sub-menu that appears, click on Personal Access Tokens.
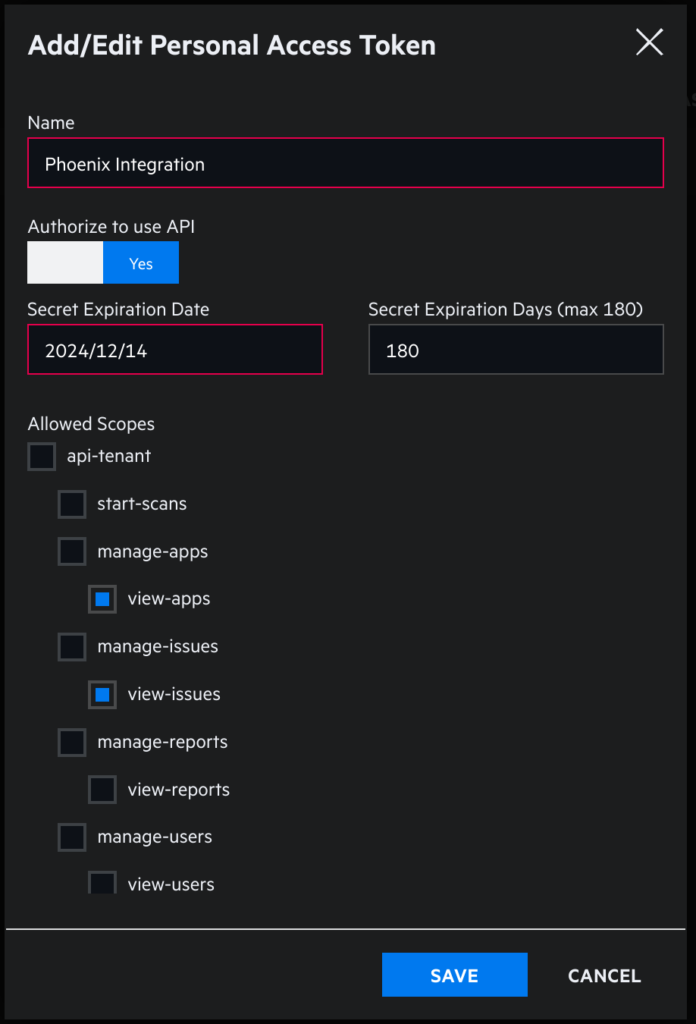
In the Personal Access Tokens page, click on “+ Add Personal Access Token” and complete the new token details. Make sure that you set the Authorize to use API switch to “Yes”, and select “view-apps” and “view-issues” under Allowed Scopes.
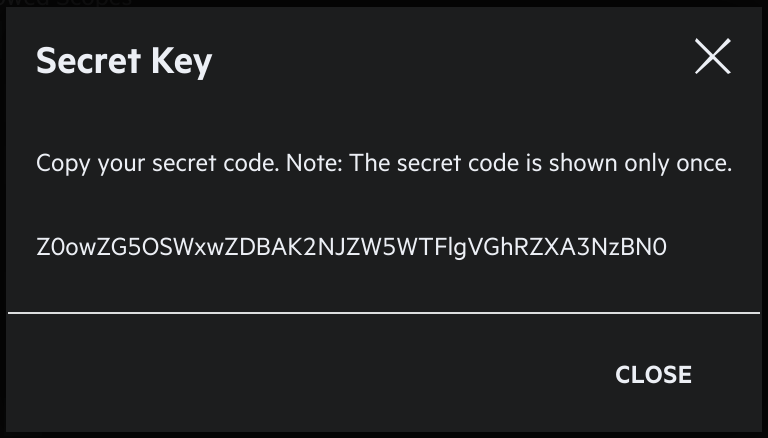
Once you have finished configuring the new service account you can save it. At this point you’ll be shown the Secret Key for the new token. It’s very important that you copy and safely store these value now, since you won’t have access to the Secret after this point.
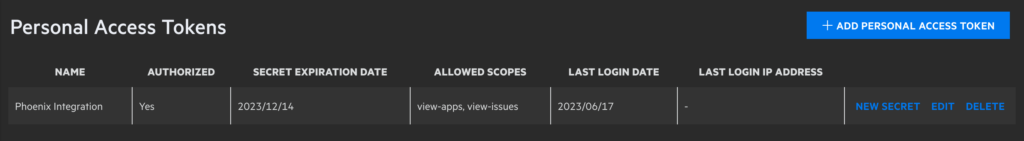
Once you close the pop-up, you should see an entry in your personal access tokens like the one below.
Now you can go to the top-right user menu and click on Account Settings. In the settings screen you can see a section with the Tenant Code. Copy this code to use later in the integration configuration.
Find you API Endpoint URL
Now that you’ve created your application’s credentials, you just need to find the API URL that should be used with your Fortify account. In order to do that you can visit the Fortify documentation page. The table below is a copy of the URL details – but the Fortify page could contain more up-to-date information.
| Data Center | API Root URL |
| AMS | https://api.ams.fortify.com |
| EMEA | https://api.emea.fortify.com |
| APAC | https://api.apac.fortify.com |
| SGP | https://api.sgp.fortify.com |
| FedRAMP | https://api.fed.fortifygov.com |
| Trial | https://api.trial.fortify.com |
Create a Fortify Integration
Within your Phoenix Security account, select Integrations > Scanners from the left menu, then locate the Fortify entry (you can filter by Cloud scanners) and click on it to create the integration.
On the next step of the process, enter the credentials created in the first part of this guide.
- Server URL: The API Root URL for your data centre – if left empty it will default to https://api.ams.fortify.com
- User Name: The username of the user that created the personal access token
- Password: The Secret Key from the personal access token
- Tenant: Your Tenant’s code
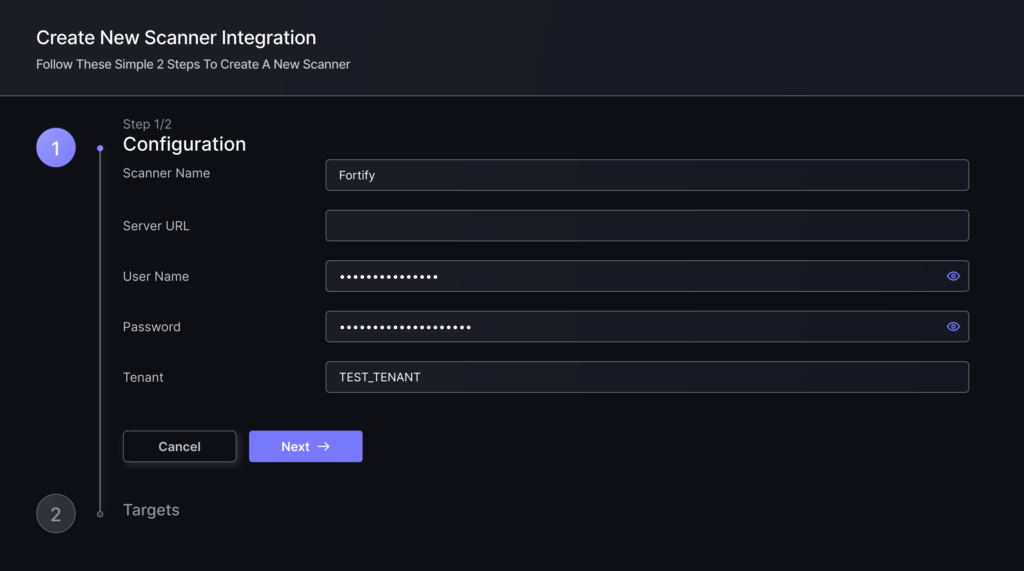
Clicking on “Next” the platform will check the credentials and present a list of Targets. In this case each target is an “application” configured in Fortify and accessible with the provided credentials. In this step you can choose whether you want to fetch from all available targets, select which ones to fetch from, or select which ones to exclude from the fetch process.
To finish the configuration click on “Create Scanner“.
Unless there are issues with the credentials, the new scanner will appear in your list of integrations (under Integrations > Scanners) and the platform will start to collect asset and vulnerability details from all selected targets.
All the scanner’s assets and vulnerabilities will be automatically added to your account’s Default Application, and will be available to start assigning them to user-created Applications as required.

