Mend.io API Credentials
To integrate with the Mend.io API you need a valid set of API Base URL, API Key and User Key. In order to gather these details, please follow the instructions below.
- Log in to Mend.io at https://saas.mend.io or https://saas.whitesourcesoftware.com
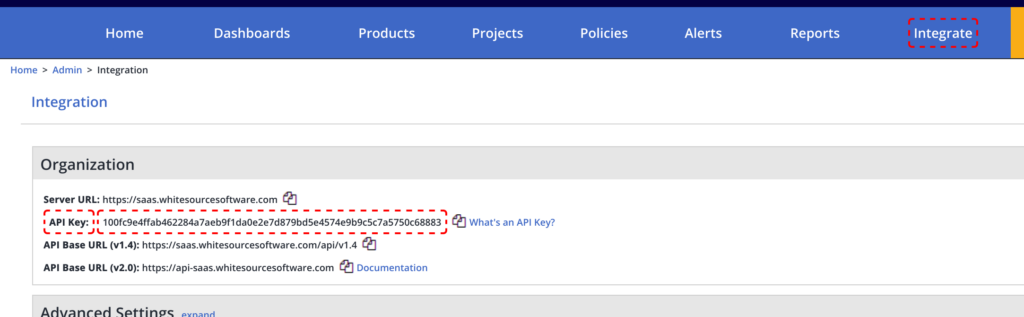
- Select Integrate from the right-side of the top menu and check the details under Integration > Organization.
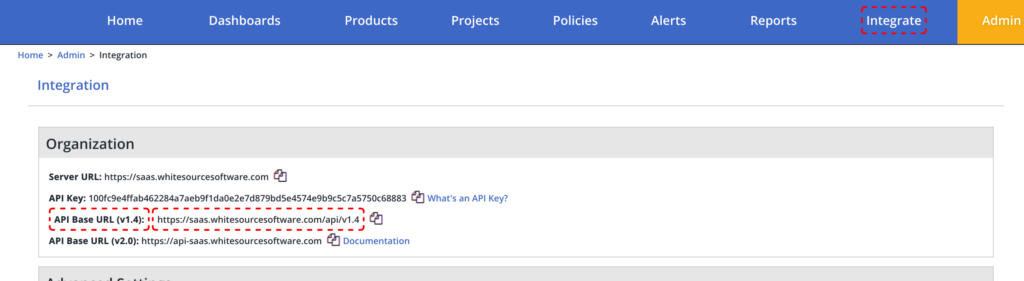
- Copy the URL next to API Base URL (v1.4)
- On the same screen, copy the API Key value.
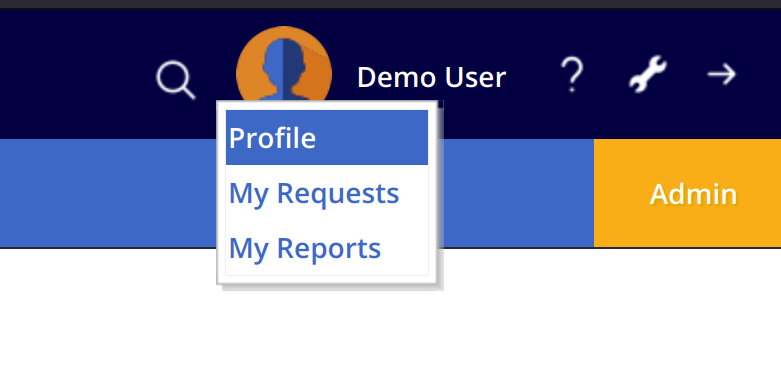
- Now click on the user menu at the top-right corner and select Profile.
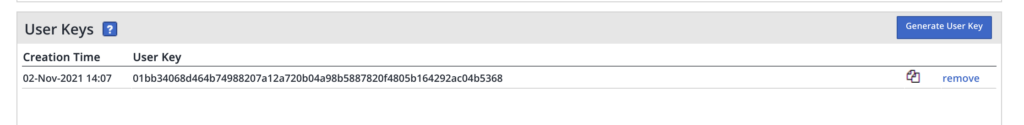
- Under User Keys click on Generate User Key and copy the new key that appears in the list.
You will need the API Base URL, API Key and User Key when configuring the integration between Phoenix Security and Mend.io.
Create a Mend.io Integration
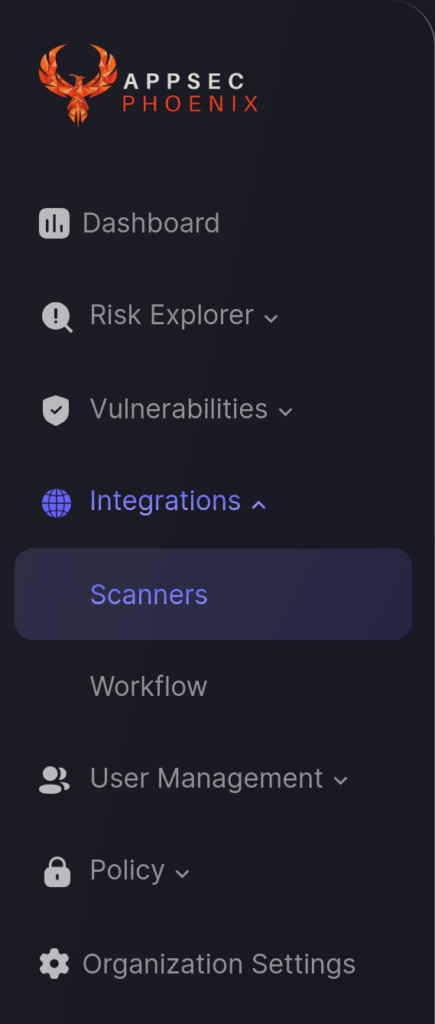
- On the sidebar menu, navigate to the Scanners tab in the Integrations section.
- Click on the “Add Scanner Integration” button on the right side of the page.
- On the second step you need to provide the required details for the scanner integration. In the case of Mend.io you need to provide:
- Name: The name for this integration.
- Server URL: This is the API Base URL collected in the previous steps.
- User Key: This is the User Key generated in the previous steps.
- Organization Token: This is the API Key from the Integration > Organization section, as described above.
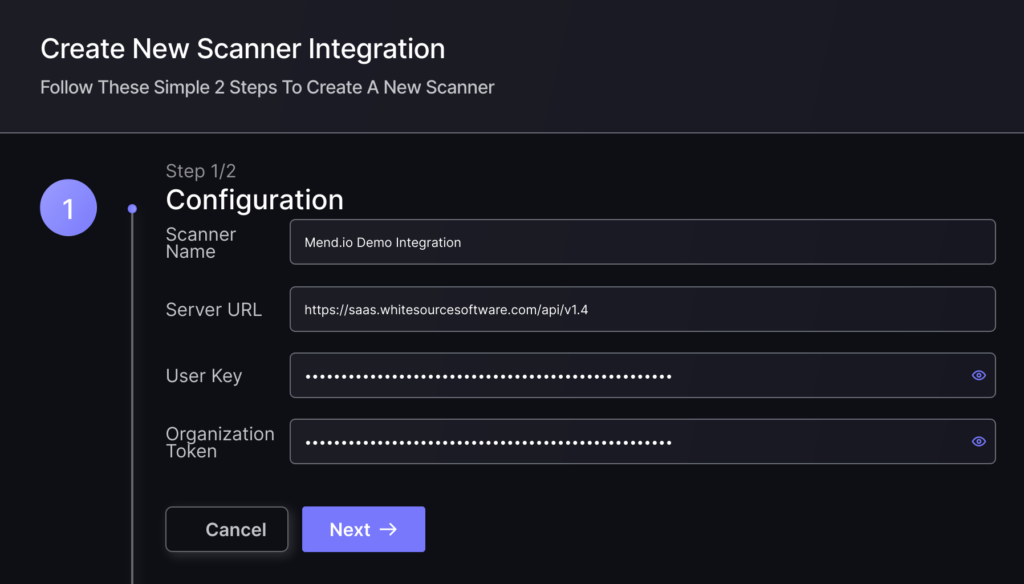
- In the next step you will be able to select whether the platform fetches all the assets and vulnerabilities available form the scanner, or you can include/exclude individual “targets” (applications, project, etc), if supported by the scanner.
- To finish the configuration click on “Create Scanner“.
Unless there are issues with the credentials, the new scanner will appear in your list of integrations (under Integrations > Scanners) and the platform will start to collect asset and vulnerability details from all Subscriptions available through the integration credentials.
All the scanner’s assets and vulnerabilities will be automatically added to your account’s Default Application, and will be available to start assigning them to user-created Applications as required.

